What is HERMES 2.1 RANSOMWARE?
Today we will find out what is HERMES 2.1 RANSOMWARE, how it works and how to delete HERMES 2.1 RANSOMWARE from your computer.
HERMES 2.1 RANSOMWARE usually infiltrates your computer while being downloaded in a bundle with a popular hacked programs or while being included in downloaded file with a bunch of other trojans.
HERMES 2.1 RANSOMWARE causes the great problems for you, such as replacing your browser starting page with malicious one, browser search redirecting, changing security settings and allowing popup advertisements to show up.
HERMES 2.1 RANSOMWARE virus accomplishes this tasks by registering virus process in startup or by automatically launching malicious sites.
You have 2 ways to remove HERMES 2.1 RANSOMWARE:

Why I recommend you to use an automatic way?
- You know only one virus name: "HERMES 2.1 RANSOMWARE", but usually you have infected by a bunch of viruses.
The UnHackMe program detects this threat and all others. - UnHackMe is quite fast! You need only 5 minutes to check your PC.
- UnHackMe uses the special features to remove hard in removal viruses. If you remove a virus manually, it can prevent deleting using a self-protecting module. If you even delete the virus, it may recreate himself by a stealthy module.
- UnHackMe is small and compatible with any antivirus.
- UnHackMe is fully free for 30-days!
Here’s how to remove HERMES 2.1 RANSOMWARE virus automatically:
STEP 1: Install UnHackMe (1 minute)
STEP 2: Scan for malware using UnHackMe (1 minute)
STEP 3: Remove HERMES 2.1 RANSOMWARE virus (3 minutes)
So it was much easier to fix such problem automatically, wasn't it?
That is why I strongly advise you to use UnHackMe for remove HERMES 2.1 RANSOMWARE redirect or other unwanted software.
How to remove HERMES 2.1 RANSOMWARE manually:
STEP 1: Check all shortcuts of your browsers on your desktop, taskbar and in the Start menu. Right click on your shortcut and change it's properties.
You can see HERMES 2.1 RANSOMWARE at the end of shortcut target (command line). Remove it and save changes.
In addition, check this command line for fake browser's trick.
For example, if a shortcut points to Google Chrome, it must have the path:
C:\Program Files (x86)\Google\Chrome\Application\chrome.exe.
Fake browser may be: …\Appdata\Roaming\HPReyos\ReyosStarter3.exe.
Also the file name may be: “chromium.exe” instead of chrome.exe.
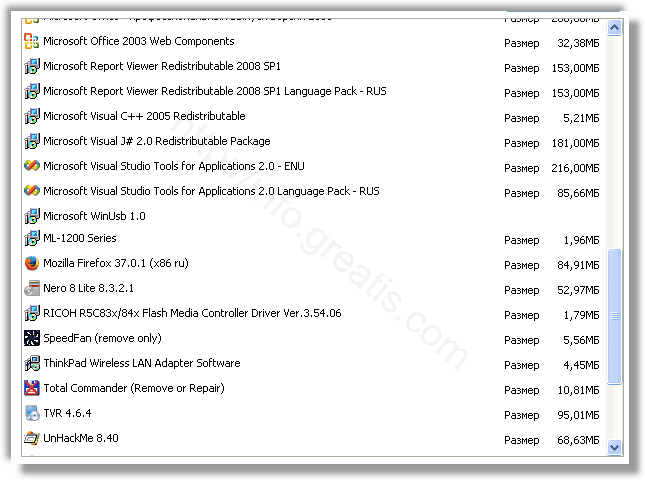
STEP 2: Investigate the list of installed programs and uninstall all unknown recently installed programs.
STEP 3: Open Task Manager and close all processes, related to HERMES 2.1 RANSOMWARE in their description. Discover the directories where such processes start. Search for random or strange file names.
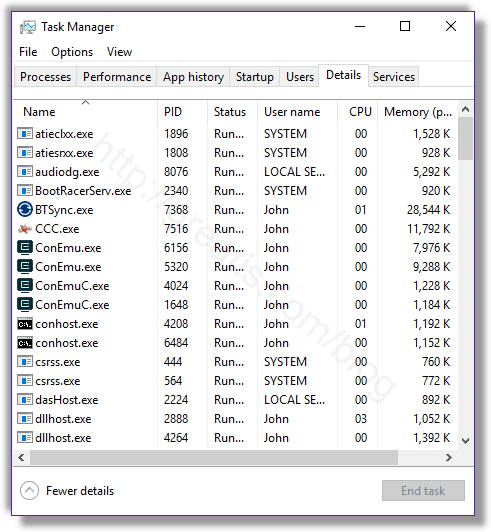
Remove HERMES 2.1 RANSOMWARE virus from running processes
STEP 4: Inspect the Windows services. Press Win+R, type in: services.msc and press OK.
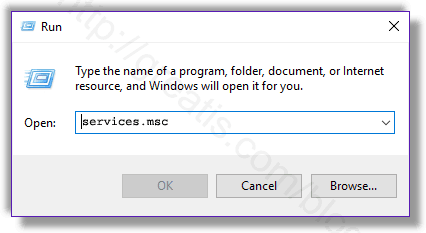
Remove HERMES 2.1 RANSOMWARE virus from Windows services
Disable the services with random names or contains HERMES 2.1 RANSOMWARE in it's name or description.
STEP 5: After that press Win+R, type in: taskschd.msc and press OK to open Windows Task Scheduler.
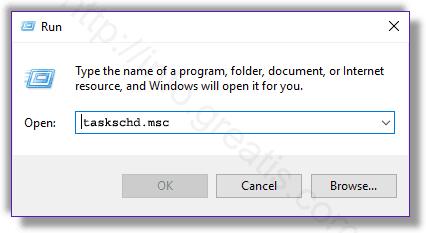
Delete any task related to HERMES 2.1 RANSOMWARE. Disable unknown tasks with random names.
STEP 6: Clear the Windows registry from HERMES 2.1 RANSOMWARE virus.
Press Win+R, type in: regedit.exe and press OK.
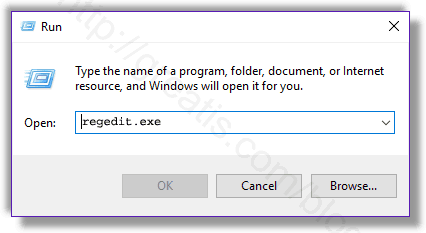
Remove HERMES 2.1 RANSOMWARE virus from Windows registry
Find and delete all keys/values contains HERMES 2.1 RANSOMWARE.
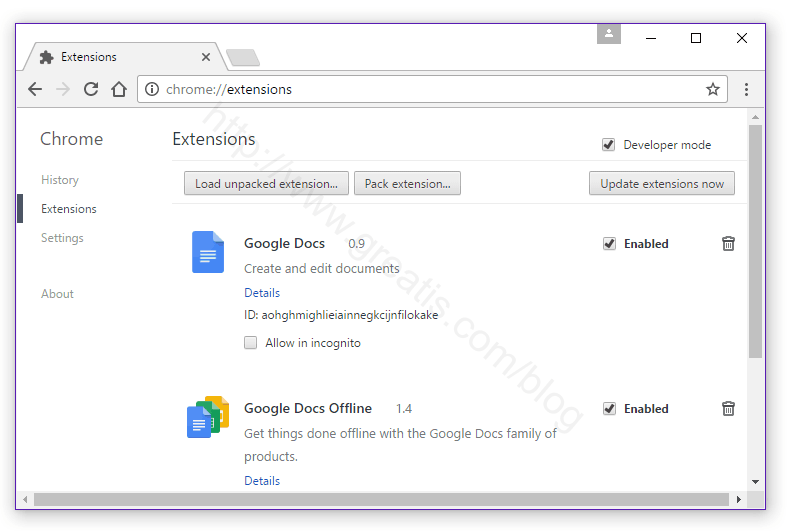
STEP 7: Remove HERMES 2.1 RANSOMWARE from Google Chrome.
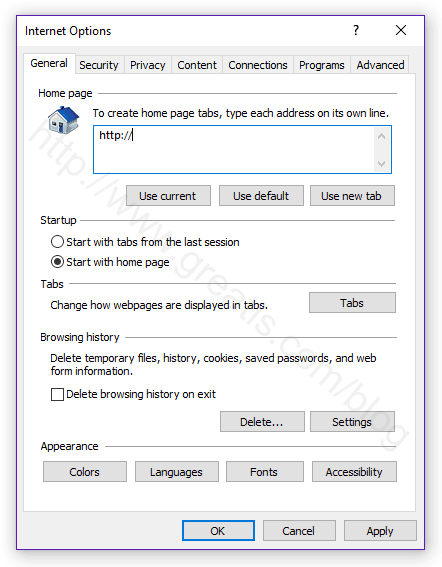
STEP 8: Remove HERMES 2.1 RANSOMWARE from Internet Explorer.
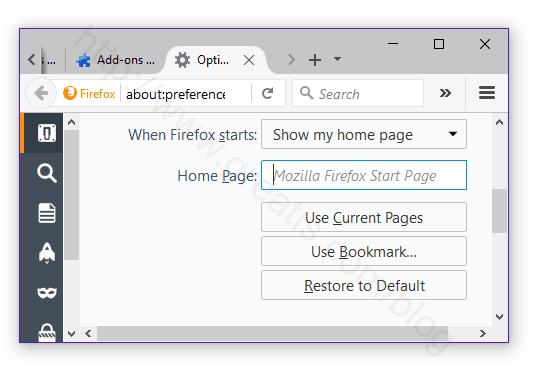
STEP 9: Remove HERMES 2.1 RANSOMWARE from Mozilla Firefox.
STEP 10: And at the end, clear your basket, temporal files, browser's cache.
But if you miss any of these steps and only one part of virus remains – it will come back again immediately or after reboot.
I use UnHackMe for cleaning ads and viruses from my friend's computers, because it is extremely fast and effective.
STEP 1: Download UnHackMe for free
UnHackMe removes Adware/Spyware/Unwanted Programs/Browser Hijackers/Search Redirectors from your PC easily. UnHackMe is compatible with most antivirus software.
UnHackMe is 100% CLEAN, which means it does not contain any form of malware, including adware, spyware, viruses, trojans and backdoors. VirusTotal (0/56).
System Requirements: Windows 2000-Windows 8.1/10 32 or 64-bit. UnHackMe uses minimum of computer resources.
STEP 2: Double click on UnHackMe_setup.exe
You will see a confirmation screen with verified publisher: Greatis Software.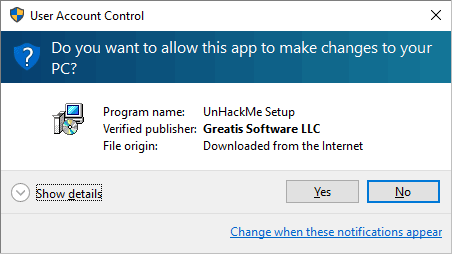
Once UnHackMe has installed the first Scan will start automatically

STEP 3: Carefully review the detected threats!
Click Remove button or False Positive.Enjoy!