How to remove REYNOT.COM virus (Removal Guide)
How to uninstall QR-CODE-GENERATOR.ONLINE virus (Removal Guide)
How to eliminate PENADEE.COM virus (Removal Guide)
How to delete NEWS-YUBIGI.COM virus (Removal Guide)
How to eliminate NEWS-FASUGU.COM virus (Removal Guide)
How to delete LPSERIALSE.CLICK virus (Removal Guide)
How to cut off LADSSTUDIO.COM virus (Removal Guide)
How to delete HILDACENTER.AZUREWEBSITES.NET virus (Removal Guide)
How to delete EARTHHEARTSMITH.TOP virus (Removal Guide)
How to cut off 1WFSON.TOP virus (Removal Guide)

GitLab released critical security updates for both its Community and Enterprise Edition, addressing a severe authentication flaw (CVE-2023-7028) that allows [...]
How to eliminate WWW.A7866.TOP virus (Removal Guide)
How to eliminate WPLNK.CC virus (Removal Guide)
How to delete WEBFIND-RIGHTAWAY.COM virus (Removal Guide)
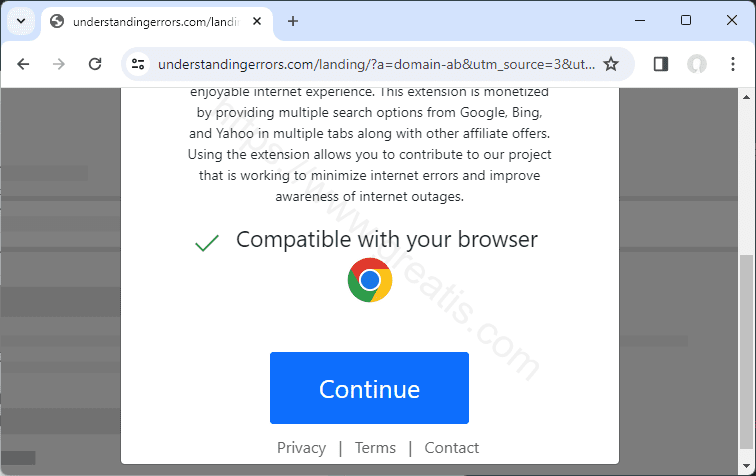
How to erase UNDERSTANDINGERRORS.COM virus (Removal Guide)
How to get rid of TONEADDS.COM virus (Removal Guide)
How to cut off RENEW-SUBSCRIPTION.INFO virus (Removal Guide)
How to erase QUALLOGESS.CO.IN virus (Removal Guide)
How to uninstall POLITICALSALE3.XYZ virus (Removal Guide)
How to get rid of PALIMPRANDRITLE.CO.IN virus (Removal Guide)
How to erase NEWS-WIMEPU.COM virus (Removal Guide)
How to delete NEWS-FIHOXE.COM virus (Removal Guide)
How to eliminate LEVUSPOWER.XYZ virus (Removal Guide)
How to eliminate HUHFIVEDIP.LIVE virus (Removal Guide)
How to get rid of GARRI-POTTER.FUN virus (Removal Guide)
How to get rid of GADSSMART.COM virus (Removal Guide)
How to delete G74P.TOP virus (Removal Guide)
How to delete FINDNSEARCH-IMMEDIATE.COM virus (Removal Guide)
How to clear away ETYRTHONRONG.INFO virus (Removal Guide)
How to uninstall DUALSALE3.XYZ virus (Removal Guide)
How to remove DESKTOPLEADS.INFO virus (Removal Guide)
How to uninstall DATE.REIFEFRAUEN.COM virus (Removal Guide)
How to cut off CUMBHA.APP virus (Removal Guide)
How to cut off CLASHANDCASH.XYZ virus (Removal Guide)
How to get rid of ATRADEST.COM virus (Removal Guide)
How to delete A.RE-CAPTHA-VERSION-3-53.TOP virus (Removal Guide)
How to uninstall 97F68628BC.NEWS-FIHOXE.COM virus (Removal Guide)
How to remove 1XLITE-579542.TOP virus (Removal Guide)
How to remove 1WZHHF.TOP virus (Removal Guide)
How to uninstall 1WVWY.TOP virus (Removal Guide)